
What You Need to Know About Hitrust Csf® Certification
HITRUST® is an organization that is responsible for creating and maintaining a common security framework in the healthcare sector, among others. Specifically, HITRUST is a certification frequently required by organizations that handle Protected Health Information.
HITRUST’s mission is to establish a holistic approach for the healthcare industry to manage information security risks.
HITRUST is actually a combination of a lot of different security standards, including HIPAA, HITECH, PCI, COBIT, NIST, FTC, and much more. As the central gatekeeper, HITRUST has become the gold standard for compliance framework in the healthcare industry. HITRUST also created the framework itself, called Common Security Framework (CSF).
In this comprehensive guide, we’ll introduce you to the complex world of HITRUST and HITRUST CSF® certification. We’ll cover what HITRUST is, what HITRUST CSF entails, and what steps, costs, and measures you need to become HITRUST CSF certified.
What’s inside this ultimate guide to HITRUST CSF certification:
- Getting to Know HITRUST Common Security Framework
- Who Should Be HITRUST Compliant?
- Why Become HITRUST CSF Certified Now?
- What Is HITRUST Exactly?
- Why HITRUST Is a Great Thing for Everyone (And Not Just the Company Getting Compliance)
- Why Should Businesses Get HITRUST CSF Certified?
- What are the main differences between HITRUST and HIPAA?
- How Long Does it Take to Become HITRUST CSF Certified?
- How Do You Get HITRUST CSF Certified?
- How Often Does HITRUST CSF Certification Occur?
- How Much Does It Cost to Get HITRUST CSF Certified?
Getting to know the HITRUST Common Security Framework (CSF)

The HITRUST Common Security Framework (CSF for short) is the most comprehensive and most widely applied security framework in the US healthcare system. It was developed and maintained by healthcare industry specialists and experts who had a common desire to design an objective and measurable means of managing healthcare security risks.
More specifically, HITRUST CSF was required to make sure that healthcare-related facilities subject to HIPAA and their 3rd party business associates meet the HIPAA requirements. Not just that, but these healthcare stakeholders must do so in a manner that offers the best data and security protection.
In today’s ever-changing healthcare security landscape, HITRUST CSF is an eclectic security framework that addresses myriads of local, national, and global regulatory, privacy, and security measures and guidelines. As such, having HITRUST CSF certification is more than a badge of recognition, it shows that you are at the forefront of safeguarding Protected Healthcare Information. And that you put the privacy and security of your patients’ sensitive information above all.
Who should be HITRUST compliant?

If a healthcare company asked if you are HITRUST CSF certified, chances are that you are asking yourself: should I hold this certification and, if yes, why?
First, let’s reiterate one point: HITRUST CSF brings together many existing internationally-recognized security standards like NIST, HIPAA, FTC, PCI, COBIT, Red Flags, and ISO.
More crucially, HITRUST provides healthcare-covered entities and their business associates with insights into how their organizations can and should handle security risks. This way, they will have clear-cut, actionable guidelines for how to take a more proactive approach to data protection and security risk mitigation.
Against this background, it’s crucial that any company that’s required to be compliant with NIST, HIPAA, FTC, PCI, COBIT, Red Flag, and ISO to also obtain the HITRUST CSF Certification. More specifically, if your company creates, accesses, stores, or exchanges personal health information, you are required to be HITRUST CSF certified and compliant.
Oftentimes that means companies and organizations such as hospitals, insurance companies, pharmacies, healthcare vendors, physician offices, and more in between should hold HITRUST CSF certification.
So, how much work is it exactly?
What does my company need to do to become HITRUST CSF certified? The simple answer is, a lot.
We’re not going to sugar-coat it: it’s a BIG deal.
As you already know, healthcare in and of itself is complex and subject to a plethora of regulatory guidelines. For a company to start the journey to HITRUST CSF certification, it must first adopt what’s called the Common Security Framework (CSF) which is frequently updated. In fact, CSF 2.0 is one recent iteration, having come a long way since its inception in 2014.
What makes the HITRUST CSF certification process a little daunting is that a company must ensure that literally hundreds of policies and procedures are created, followed, documented, and implemented.
The assessment stage alone can last between two and eight weeks depending on the intricacy of the healthcare information the company is handling as well as the scope environment and the complexity of the organization itself. What’s more, HITRUST CSF certified companies must also be using the right technologies and protocols in order to stay compliant.
As you can see, it’s a lot of work, not to mention the price tag associated with the whole process. However, the lack of HITRUST compliance can lead to devastating ramifications for the company.
Remember HITRUST CSF is a single-source compliance and regulatory framework that encompasses ISO 27001, HITECH, EU GDPR rules, an array of other industry frameworks, and state-specific laws. The process is not the same for every company.
Schedule Your Free Consultation
Looking To Meet Now? Schedule A Meeting Today
Why become HITRUST CSF certified now?
HITRUST compliance is now more important for healthcare-covered companies and their business associates than ever – and for good reason. The number of incidents of personal information being exposed and private health information being seen by those not authorized is rising, creating a huge risk for healthcare players.
Get this: A cyber-attack happens every 39 seconds.
Hackers attack Internet-connected computers and devices every 39 seconds (according to a comprehensive study by Clark School at the University of Maryland). In fact, computers under the study were attacked thousands of times a day. Interestingly, the attacks are indiscriminate and don’t target a particular institution, which means healthcare companies are more prone to security breaches and cyber-attacks than ever.
Digital healthcare is on the rise, making it more of a target to cyber-attacks.
Startup funding for digital healthcare is expected to double in the US over the next three years, growing from $3.5 billion in 2014 to $6.5 billion by the end of 2017, according to a recent Accenture study.
The growth in these types of startups will largely be driven by evolving consumer expectations, Accenture explained. While digital healthcare is a welcome move for the industry, it also exposes hospitals, insurers, care facilities, and other healthcare companies to the great risk of cybercrime.
That’s why it comes as no big surprise that in recent years healthcare has become a lucrative target for hackers using phishing emails, weaponized ransomware, and misconfigured cloud storage buckets.
Hackers are becoming smart and they just keep tweaking their method

It’s now more important to become HITRUST compliant to keep abreast of changing hackers tacts. Take US State Department, for instance; in 2015, the Wall Street Journal revealed that they’d fallen victim to an email hacking attack. Despite putting a state of the art security system in place, the State Department often grapple with hackers who still get access to their unclassified material. So, if the whole State Department can’t fend off these ever-evolving hacking attacks, how can healthcare companies fair on?
What HITRUST CSF certification really is

HITRUST CSF helps clarify and/or add onto what HIPAA requirements suggest. Remember HIPAA doesn’t necessarily provide enough detail. For example, it may say things like “reasonable & appropriate” protections.
That’s where HITRUST CSF certification comes into play. It’s a very specific and descriptive framework to help healthcare companies manage security needs required by HIPAA, ISO, NIST, and other industry standards. When all’s said and done, however, the primary goals of HITRUST CSF is to help ensure a company is HIPAA compliant.
Why HITRUST is a great thing for everyone (not just the company getting compliance):
Yes, hospital, healthcare insurance firms, pharmacies, doctors offices, and vendors need HITRUST CSF certification to stay in compliance. But HITRUST compliance is a great thing for everyone. And here is why:
1. It’s a common framework for security and compliance
When someone says they are HITRUST CSF certified, anyone in healthcare will know what it means. That’s because everyone who is certified has gone through the same rigorous process
2. Keeps personal health data more secure
If you aren’t willing to protect your patients’ personal data, you have no business in the healthcare industry. In the digital age, keeping personal health data more secure should be the #1 priority.
3. Lock out fly-by-nights
HITRUST helps keep the bad companies out who don’t seem to care about personal data security and compliance from touching sensitive/protected healthcare information.
Why should businesses get HITRUST CSF certified?
If you are a healthcare-covered business, getting HITRUST CSF certification is a no-brainer. And with good reasons:
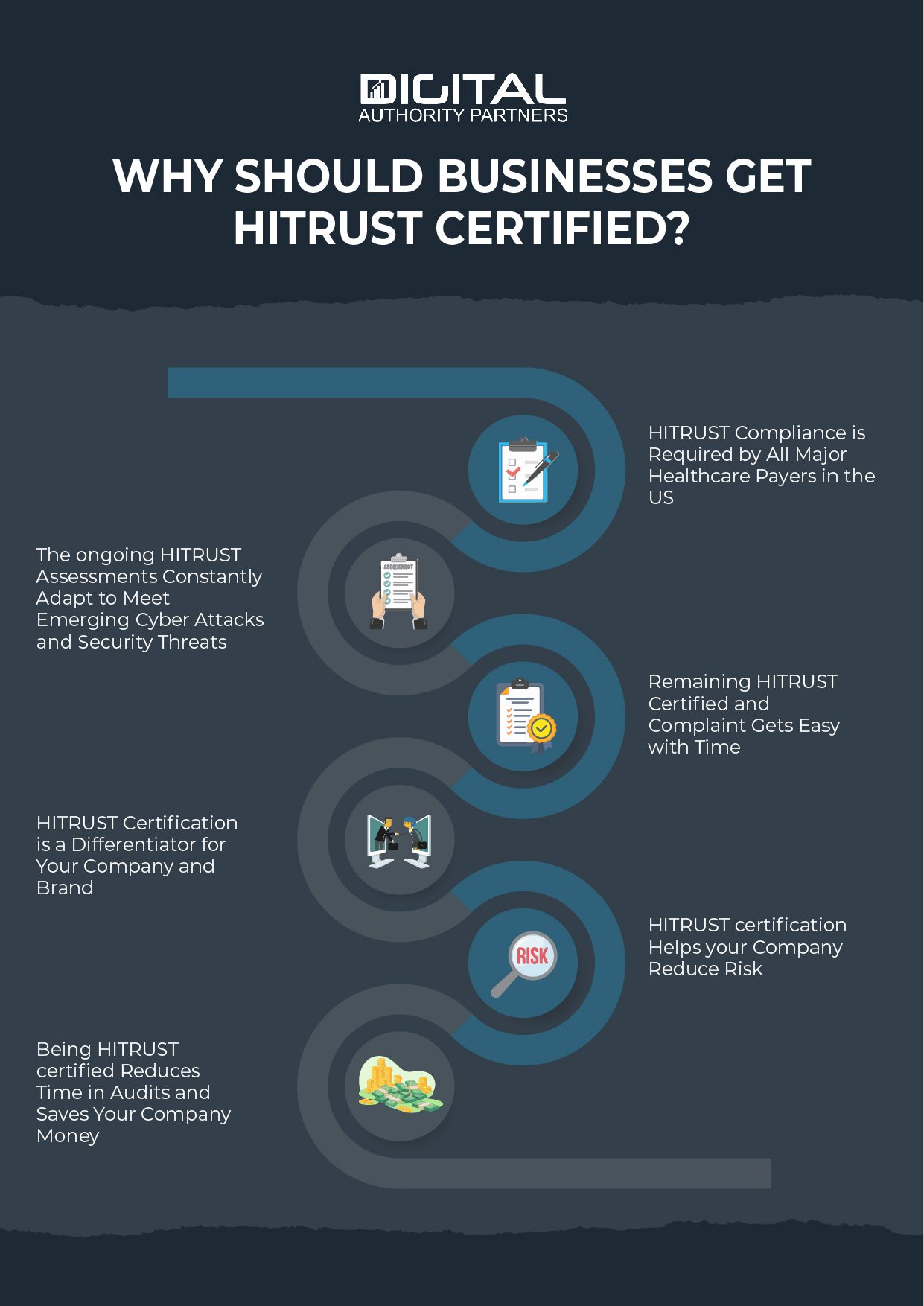
1. HITRUST compliance is required by all major healthcare payers in the US
No matter what your business does in the healthcare realm, it’s crucial to know that HITRUST CSF certification is often required. In fact, most major healthcare payers require that their business associates must be HITRUST CSF certified. What’s more is that right now over 90 other healthcare payers call for their 3rd party service providers (aka Business Associates) to get HITRUST CSF certification. With that in mind, HITRUST compliance is a great way to stay in the positive light in payers’ eyes.
2. The ongoing assessments constantly adapt to meet emerging cyber attacks and security threats
HITRUST CSF is revised and updated regularly to make sure that healthcare organizations are always up-to-date in the face of security risks and the introduction of new regulatory guidelines. With this approach of continuous improvement and review, CSF is constantly enhanced and adapted to meet emerging cyber-attacks and security threats. As such, HITRUST CSF is clearly the future and a great way for healthcare organizations to put their best foot forward. So, get on the bandwagon early or ignore it at your peril.
3. Remaining HITRUST CSF certified and complaint gets easier with time
The process is great! Generally, you do the same repeatable process every time, leading to better, more reliable, and more efficient business results. The good thing is that HITRUST provides a step-by-step process or roadmap that’s repeatable for everyone, which means you can do things right every time.
Another plus is that the HITRUST CSF certification process is well documented, and there are a ton of resources online that can help you stay on top of every step. Oftentimes that also means that when you lose employees, you don’t need to reinvent the wheel. Just make sure that your new employee follows the same process everyone has been following. More importantly, the same docs, procedures, etc. are all required, so the chances are that you have them on hand.
4. HITRUST CSF certification is a differentiator for your company and brand
In today’s ever-competitive business environment, it’s quite challenging to make your brand and company stand out. The good news is that getting HITRUST CSF certified can help make your brand stand out from a sea of competition. And given that it offers one view of your entire certification, you’ll beat your beat your competitors to the punch. Even better, HITRUST CSF certification showcases that your company is strong, vibrant, and fully committed to security compliance.
5. HITRUST CSF certification helps your company reduce risk
Keeping a tab on personal information risk and compliance is a top goal for most healthcare companies, and there are many ways HITRUST CSF certification can help you mitigate or reduce security risk by a huge margin:
-
- Reduce risk through better information security. HITRUST certificate enables companies to set up better information security frameworks and measures to ensure maximum results.
- Helps ensure proper security of your patient information, IP, and any other proprietary data. This is crucial because any breach can lead to insurmountable financial, reputational, and social consequences.
-
Schedule Your Free Consultation
Looking To Meet Now? Schedule A Meeting Today
- Lower security risk for those with HITRUST CSF certification. Having better information security, in return, will help provide improved coverage and reductions in cyber insurance premiums. It’s a win-win for the company.
6. Being HITRUST CSF certified reduces time in audits and saves your company money
Let’s face it; compliance audits can be a pain in the rear. They can usurp all your precious time, resources, and efforts that you could be putting to good use. That’s where HITRUST CSF certification comes in handy. Given that it’s wide-ranging and all-encompassing, getting HITRUST CSF certified gives your company a headstart for ALL other frameworks and certifications, something that’ll cut time in audits by a big margin.
It’s worth noting that the HITRUST CSF certification process is so stringent that it allows you to qualify for all sorts of frameworks/certifications such as PCI, HIPAA, NIST, and a lot more in between.
What are the main similarities and differences between HITRUST and HIPAA?
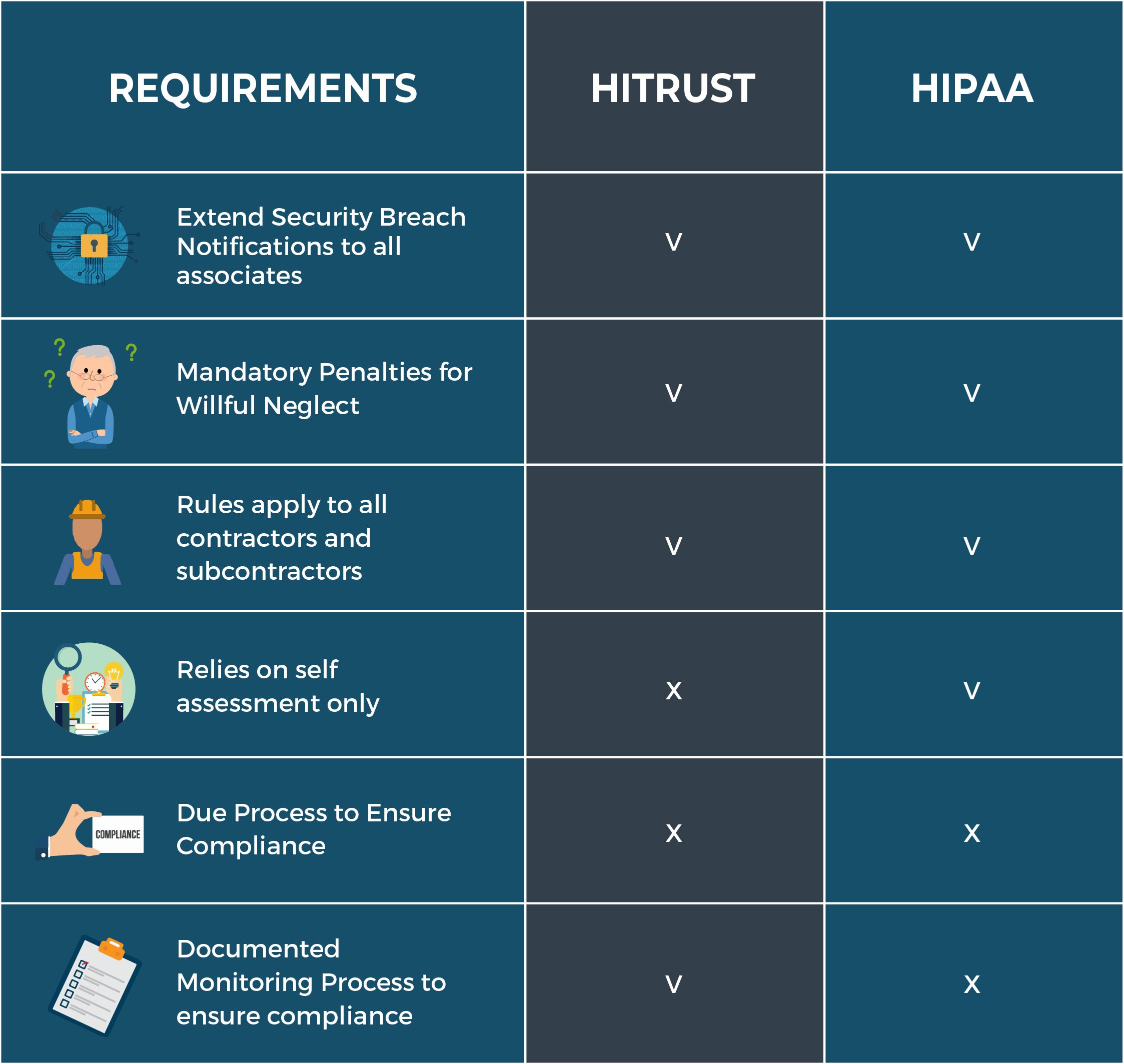
HIPAA is short for Health Insurance Portability and Accountability Act. HIPAA in and of itself is an Act of law that sets out to protect patient medical records. In practice, HIPAA provides the patients with a certain level of privacy when it comes to why, when, and who can access their personal data stored by healthcare organizations.
The truth of the matter, however, is that whether a company is HIPAA compliant or not is subjective without an actual certification process. In other words, a healthcare provider or its business associates can say they are HIPAA compliant without adhering to part or all of the laws laid out by HIPAA.
With that being said, there’s no such thing as “HIPAA-compliant” as there is no due process or real status.
For all intent and purposes, HITRUST is the closest you can get to being “HIPAA compliant.” After all, HITRUST CSF is the ONLY certifiable framework that rounds up other frameworks, including ISO, PSI, NIST, and HIPAA.
HIPAA is all about self-auditing and assessment.
So, if someone asks, “Are you HIPAA compliant?,” the best you can do is point them to your HITRUST CSF certification which uses the third-party audits to ensure compliance. More importantly, at the core of HITRUST is the certifiable CSF that provides healthcare entities with a flexible, efficient, and comprehensive approach to risk management and regulatory compliance.
How long does it take to become HITRUST CSF certified?

HITRUST CSF assessment and certification encompasses 19 different domains and 135 required controls. It’s only when all these controls are entirely implemented that an organization can become fully HITRUST CSF certified. To that end, the length of time required depends on its level of readiness and amount of measures to be taken to implement the controls in the scoped environment.
For most companies, the first step would be to conduct a thorough self-assessment to determine if they are ready for certification or not. Some of them might go the extra mile and invite an external CSF specialist to assess their readiness. Either way, the biggest length of time is for an organization to get ready for the 3rd party audit to review and implement all required processes and controls.
Initial assessment takes between 2 weeks and 8 weeks
The initial self-assessment usually takes up to a few weeks, followed by an independent assessment (by a 3rd party). In all, the assessment itself should take between 2 and 8 weeks on average depending on how complex your organization is, its size, and the scoped environment.
6 More weeks for validation, 3 to 4 months total
Once the self and 3rd party assessments have been carried out, it can take up to 6 more weeks for the validation to take place and finally get certified. In total, once an organization is ready and set for the assessment, it can take between 3 and 4 months to conduct, validate, and finalize the assessment, as well as get HITRUST CSF certification.
How do you get HITRUST CSF certified?
Getting HITRUST CSF Certification follows a clear-cut process with few or no shortcuts at all. Here are 7 key steps that you need to traverse to ensure that your HITRUST CSF certification process is least painful and hassle-free.

Step #1. Adopt the Common Security Framework
Common Security Framework (CSF) is what’s certifiable and at the heart of HITRUST CSF certification (and, of course, helps prove HIPAA compliance). When adopting CSF, it’s prudent to understand that it’s divided into 19 different domains, namely:
- Information Protection Program
- Endpoint Protection
- Portable Media Security
- Mobile Device Security
- Wireless Protection
- Configuration Management
- Vulnerability Management
- Network Protection
- Transmission Protection
- Password Management
- Access Control
- Audit Logging & Monitoring
- Education, Training & Awareness
- Third Party Security
- Incident Management
- Business Continuity & Disaster Recovery
- Risk Management
- Physical & Environmental Security
- Data Protection & Privacy
Also, unlike the HIPAA framework that creates broad buckets such as Security Controls and Administrative Controls, HITRUST Common Security Framework doesn’t. A would-be HITRUST compliant organization should adopt the CSF in its entirety to prove compliance.
Step #2. Adopt the policies/procedures outlined by HITRUST
Besides the above-mentioned 19 domains, HITRUST CSF outlines 135 (previously 64) security controls, 700+ requirements and 42 control objectives that you need to meet. These are clearly set procedures or policies that healthcare organizations must adapt to become HITRUST CSF certified. This is a matter of all or nothing, which means that you have to adopt ALL 135 security controls to get up to HITRUST scratch.
Step #3. Implement the right set of technologies
Again, you must use the right set of technologies in order to be HITRUST CSF certified. Gone are the days when healthcare providers had to use simple databases to store and access sensitive patient information. They now have to use a raft of advanced technologies and robust software to ensure the utmost security of personal data. What this simply means is to leverage technologies and solutions that have achieved HITRUST CSF Certification status themselves. It is always easy to know if a technology is indeed HITRUST CSF certified because the developer often makes it known far and wide.
Step #4. Document all of your policies, risk assessments & technical configurations
A significant volume of documentation is involved during the assessment, validation, and completion stages. These include policies, risk assessments, as well as technical configurations, and documentation. If it is your first time seeking HITRUST CSF certification, dealing with all these pieces of documentation can take around 3-6 months. In your subsequent audits, you can expect the whole documentation process to last approximately 60 days depending on the complexity of your organization and the full scope of the audit environment.
Step #5. Conduct a self-audit or readiness assessment
HITRUST provides you with the option to do your own self-assessment in order to gauge your readiness for an actual 3rd party assessment. In fact, it is highly recommended that you first perform a thorough self-audit and assessment. The good news is that there are nifty self-assessment tools out there that you can use on regular basis to make the whole process effortlessly easy and effective.
The main goal of a self-audit is to find out any gaps in regulatory compliance and security risks that you can reduce or address before the actual CSF audit and assessment is conducted. Otherwise put, a self-assessment can help you make necessary changes before the CSF assessor arrives to do the validated assessment. Of course, if you think that you are good to go, you can welcome a CSF assessor to conduct a validated assessment right away.
Step #6. Determine who your CSF assessor will be
The CSF assessment can take between 4-5 weeks, which is why you need to bring a worthy CSF assessor to make it even easier. To zero in on the best assessor, you need to get recommendations from other industry players and carry out a few interviews. Make sure to work with a HITRUST approved assessor with a clean track record of delivery.
Once you have hired the right CSF assessor, you can now conduct an on-site comprehensive audit by a 3rd party. A good example would be Coalfire.
Step #7. Certify your CSF with HITRUST
This is the moment of reckoning. After all your efforts to clean up your security procedures, self-audit, and adopting CSF, it’s high time you call in the folks from HITRUST to actually certify it as well. After all, that is the only way you’ll obtain “HITRUST CSF Certified” status.
This is a stage of the process that calls for some patience. Remember this is the lengthiest portion of the HITRUST CSF certification process which can take up to 18 months. And given that CSF is becoming the gold standard for HIPAA, ISO, and NIST compliance, HITRUST specialists are always dealing with a huge backlog of requests.
How often does HITRUST CSF certification occur?

Considering that data security and risk management is ever-evolving in the face of increasing cyber-attacks, advancing technologies, and changing regulations, the whole HITRUST CSF certification process has to be repeated every year. The good thing is that it becomes much easier, faster, and potentially cheaper each time going forward.
How much does it cost to get HITRUST CSF certified?

Cost is one of the major factors for companies gunning for HITRUST CSF certification. So, how much does the HITRUST CSF certification process cost an organization in 2019? It all boils down to what steps you’ll take to get HITRUST CSF certified. Well, here’s the thing: HITRUST CSF certification isn’t cheap or easy, and justifiably so.
The costs a company have to foot in order to get HITRUST CSF certified have increased in recent years because CSF has evolved and the certification process has become a little more complex each passing years. These costs are often placed into two categories: direct and indirect costs.
1. Direct costs for HITRUST CSF certification are around $60,000 – $120,000
The direct cost for HITRUST CSF certification process is approximately $60K – $120K at the low-tier; however, the costs can be far much higher for larger healthcare companies, pharmaceutical firms, insurers, and big hospitals with large patient volumes. It’s all about the size and complexity of the organization. These direct costs include the assessor fees which can range from in the tends of thousands of dollars.
2. Self-audit / assessment costs
Carrying out an initial self-audit can do wonders for the entire HITRUST CSF certification process. Although it is an optional step, you can gain insights on how to improve the security framework and better adhere to regulatory compliance before the actual assessment.
If you use self-assessment tools such as myCSF, you can expect to shell out $2,500 for access to the platform for 90 days (which is plenty for self-audit). Also, you might have to pay an extra $3,750 to submit the self-audit report for scoring. If the self-audit period lasts more than 90 days, you will probably have to pay more to continue accessing myCSF. Of course, this doesn’t take into consideration any valuable time and resources you need to conduct the self-audit.
3. Indirect costs for HITRUST CSF certification
Given the nature of the healthcare organizations and the assessment process, it can be difficult to quantify the indirect costs. Of more importance is that you need to account for time spent between each audit to take care of arising issues and make sure to bring everything to compliance. Indirectly expect this to be at least 400 hrs of work.
Using conservative figures, you can estimate the cost of each work hour to be $100 per hour. However, with the costs of benefits, wages, and lost business opportunities from the actual assessment, audit, validation, and certification, this figure can be even higher.
Crunching from the above numbers, the actual cost of the HITRUST CSF assessment and certification can come to a total of $100K – $160K depending on the size of the organization.
Does your company work in the healthcare development space? Then check out our ultimate guide to building an amazing health mobile app.
| |
Want To Meet Our Expert Team?
Book a meeting directly here





